What is Atreus?
Atreus is a powerful application fraud detection tool.
What is Application Fraud?
In simple terms, Application Fraud is the deceptive practice of providing incomplete, inaccurate, fabricated or stolen information with an intent to defraud the service provider. It’s simple and it’s pervasive. To be more technical, application fraud can be classified into two categories: First Party Fraud: those deliberately providing inaccurate or fabricated information; and Third party fraud: those that are stolen from another citizen (Identity Theft) or hijacked from a legitimate customer (Account Takeover).
Application fraud, often classified under subscription fraud, is quite often the weakest link in the defense against all forms of fraud. A vast majority of the secondary fraud (e.g. PRS Fraud, IRSF Fraud etc in Telecoms) are pulled off by succeeding in defrauding the service provider through falsified or fabricated applications.
How is Application Fraud pulled off?
Relatively easily than you might imagine.
Fake, synthetic and stolen identities are fraudster’s favourite instruments. However, in our experience, fraudsters mostly use their own identity but with subtle changes in personal details to circumvent normal credit bureau checks; For instance, there are over a dozen different ways to write the name Mohamed Ali Husein with a single proof – Mohamed Husein, Mohamed Ali, Mohamed A Husein, M. A. Husein, Muhammad Hussein and so on. Imagine the same with Address and other personal details. In one fraud loss case we uncovered that used standard credit checks brought out the name Liz, Eliza, Elisa, Elizabeth, Beth and so on in over 10 attempted phone connections in a single day using a single proof of ID.
Fraudsters go further by providing legitimate details but remain on a ‘sleeper mode’ – behaving as a good customer for a few months – and then bust-out with a large unpaid bill.
How bad is the problem?
Application fraud is a serious problem. Financial services, Insurance and Telecom industries take the biggest strike in terms of losses that run into billions each year. To put it in perspective, CIFAS, UK’s Fraud Prevention Service, reported that there were over 140,000 reported ‘Application Fraud’ related cases in the UK in 2013 and identity crime (third party fraud) accounted for over 60% of all frauds.
The US Department of Justice, in their August 2014 report, published that over 11 million Americans were affected by identity theft. The vast majority of them were in turn used to defraud service providers with losses amounting to over $24 billion. According to the AITE Report: “First-Party Fraud: The Global Battle against Diabolical Charge-Offs”, first-party fraud will be responsible for an estimated loss of $28.6 billion by 2016.
The numbers are staggering. A case in point is that this fraud is despite the pervasive use of credit bureau databases at the point of application.
How can fraudsters perpetrate application fraud when I have good credit controls in place?
Majority of the banks, insurance companies and telecommunication service providers rely on credit bureau data providers for background name and address checks at the point of application. Credit scorecards are the preferred application vetting mechanism in the developed markets. However, they are a distant prospect for most developing economies struggling to maintain a reliable record of consumer credit data over time. Often times, service providers rely on foot soldiers for physical verification at best and unreliable identity proofs at worst. While the scorecards and the physical verifications help, to reduce the risk of lending, they are both far from being ideal fraud prevention tools.
Take for example, an application with a stolen identity – the person “applying” will have accurate data matching against the credit bureau data resulting in a high score, however, the person applying will not be responsible for future payments. It is the account holder whose identity has been stolen who bears the brunt of this fraud. The same will also apply to applicants providing legitimate details – again passing the credit score with flying colors – but have no intention to pay for the services. Furthermore, majority of the records in credit bureau are slightly out of date (in some cases up to 30 days) and that is plenty of time for a fraudster to catch up even after a default or write off by the service provider.
In the examples above, it goes to show that credit scorecards and physical checks, by themselves, are not very effective at curtailing fraud at the point of application.
So how does Atreus help in closing this gap?
Atreus, put simply, will do a fraud check before the application is approved. It will make use of the full spectrum of data available at a service provider’s disposal – confirmed fraudsters, suspected applications, previous attempted connections, bad debts, customers with irregular payments, cross industry fraud data and good customer data (to check for identity theft or account hijack) to ensure that no fraudster is let through the cracks of the mundane application process.
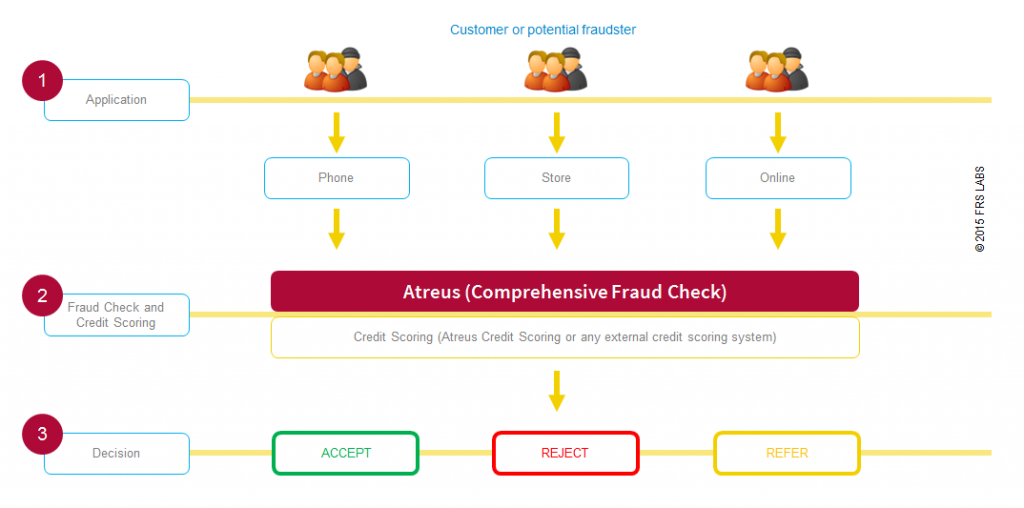
If a known fraudster or a customer who has repeatedly not paid his or her credit invoice balances come up for a new connection, the application will be matched with historical bad debt records and a Reject or Refer decision will be shown to the staff at a retail store so action can be taken before services can commence.
Besides, if a fraud check confirms an applicant to be highly risky or fraudulent there is no need for further credit bureau checks thereby saving significant amount of money on credit scorecard payments.
How does Atreus work?
Atreus works by using cutting edge fuzzy matching on credit history data to bring better and faster match results – name, address, date of birth, bank account, email, telephone (any data can be used for matching and linking application data). Atreus, through its API, provides a fully automated real time solution for instant accept, reject or refer decisions at the point of application.
Atreus also has an advanced workflow for multi-user application verifications with sophisticated search tools for higher productivity. The intuitive graphical user interface provides network maps to help identify hidden matches and sleeper fraud patterns at a glance.
How long does Atreus take for a fraud check in real time?
Atreus takes approximately 3 – 5 seconds for a real time fraud check. The fraud checks and the decisions are seamless and can be integrated into any existing point of sale or online application.
I have a pretty good Fraud Management System. Why do I need Atreus?
The Fraud Management Systems are designed to detect fraud once the customer starts using your products or services. However, they do not prevent fraud from occurring in the first place. Imagine you are granting an overdraft or a loan for $5000 or giving away a subsidized phone that costs $700; its upfront losses such as this that Atreus is designed to prevent. Isn’t prevention better than cure? Evidence from our clients points out that the fraud savings through prevention is far greater than those through detection.
How can Atreus be integrated into my existing Point of Sale (POS) retail system and/or online system?
Atreus is easy to integrate with existing point of sale applications. It comes with a RESTful API (Application Programming Interface) which can be invoked directly or through a middleware application (e.g. TIBCO). We will of course be with you every step of the way for a smooth integration.
Can Atreus be used just as a back office system without integration?
Yes of course. You can simply install Atreus on a single server or PC and start using it straight away. Atreus comes with a data integration tool which can map source data into the Atreus database. No third party software tools are required to get started with Atreus. Analysts can access the Atreus application via their browsers.
Can I schedule a demo?
Yes of course. Just drop us your details and a preferred meeting time to info@frslabs.com.